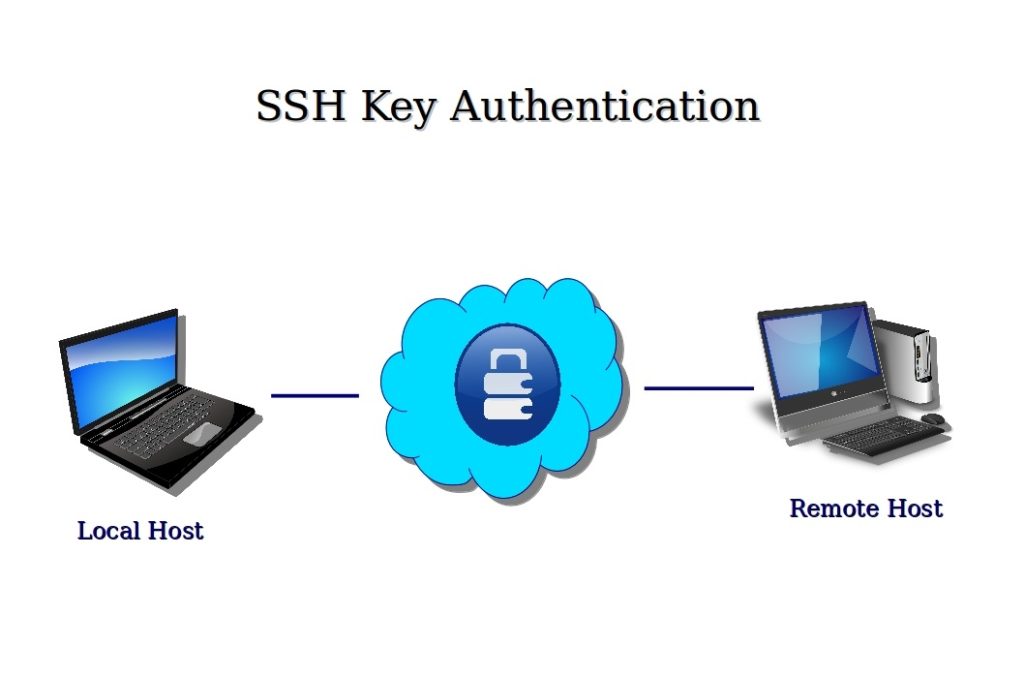
SSH allows for both password based authentication, as well as public key authentication. Public key authentication is generally regarded as being more secure, as it isn’t as prone to brute force login attempts (if you disable password based authentication). The private key can also have a passphrase associated with it, which makes public key authentication even more secure if needed.
Sometimes cloud servers will let you put a public key in as a authorized authentication key when the cloud server is created, preventing the need for password based authentication to be enabled by default.
Generate a new SSH public and private key pair:
$ ssh-keygen -t rsa -C "identifying comment" -f keypair
“Identifying comment” can be any string that will assist in determining which key this is. “username@hostname” of the machine where you are connecting from would be a good example.
eg:
$ ssh-keygen -t rsa -C "identifying comment" -f keypair Generating public/private rsa key pair. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in keypair. Your public key has been saved in keypair.pub. The key fingerprint is: 54:91:95:a1:6c:c9:dc:69:22:a4:04:6a:af:1b:f7:1d identifying comment The key's randomart image is: +--[ RSA 2048]----+ | ... . o+oo | | . . o =.+.. | | o . o O + | | . . . o o | | . S | | . | | o . E | | + . . . | | . . . | +-----------------+ $
This will generate two files, “keypair” and “keypair.pub”. “keypair” being the private key that you need to keep secure, and “keypair.pub” being the public key, that can be put on servers that you want to be able to log into with the private key.
Change the filename to suit your needs. This example uses “keypair” for the examples.
The contents of the public key file “keypair.pub” can be inserted into the ~/.ssh/authorized_keys file on the machine that you want to be able to connect into remotely. This must be done for the specific user.
Insert public key into authorized keys
View the contents of the public key file:
$ cat keypair.pub
eg:
$ cat keypair.pub ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDGZyIXXpdrvMJNPvC+Mk6ziW8TRQWCQCzWq7CU4FkssTC1/p4INbEsaeC6ZS4w810QnAtzdWDgqm5u7GeJ8HNQUvTTGSLITtqzXSSDyuRq+qJehTlRQSklHWoviYwZoflz6yh6vSP9uDE9Xh75PfMBTHETVt3nqhQ/lGkrPdog6oo+F8r5rFQpjMatYKdbfsma/pVzORQnBMuaqGRCnFtqWu5mMJvUUa3Nzu07PH7lUHU8tra124OtJrOIBJfG7k0iFMmKS3v9kvNLFvymHtEDn4noclQsJ+5FQEe7BebhZwyhGxzscM0U3mTtfPd8wtwqQNLPmDr+/q8b4r23w5fR identifying comment $
Take note of the output, and copy it into the clipboard if possible, or use some other method to get this file/data onto the remote machine, as it will be used in the next step.
On the remote server you want to be able to log into:
$ echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDGZyIXXpdrvMJNPvC+Mk6ziW8TRQWCQCzWq7CU4FkssTC1/p4INbEsaeC6ZS4w810QnAtzdWDgqm5u7GeJ8HNQUvTTGSLITtqzXSSDyuRq+qJehTlRQSklHWoviYwZoflz6yh6vSP9uDE9Xh75PfMBTHETVt3nqhQ/lGkrPdog6oo+F8r5rFQpjMatYKdbfsma/pVzORQnBMuaqGRCnFtqWu5mMJvUUa3Nzu07PH7lUHU8tra124OtJrOIBJfG7k0iFMmKS3v9kvNLFvymHtEDn4noclQsJ+5FQEe7BebhZwyhGxzscM0U3mTtfPd8wtwqQNLPmDr+/q8b4r23w5fR identifying comment" >> ~/.ssh/authorized_keys
If you have chosen to copy the public key file to the remote host instead, you can issue the following command instead:
$ cat keypair.pub >> ~/.ssh/authorized_keys
Logging into remote ssh server using the private key file
To connect to the remote host using SSH you can use the following command:
$ ssh -i keypair user@hostname
This will use the private key called “keypair” created earlier, and assuming the remote server has the public key added to the “user” users authorized_keys file, you should be able to log into the remote system.