Posted inVirtualization
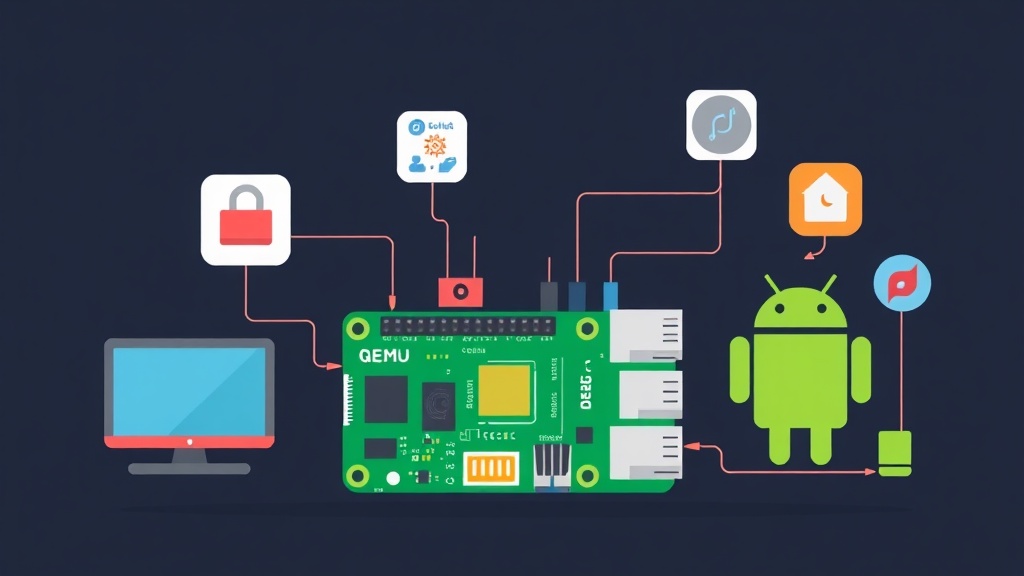
QEMU ARM64 Emulation on Linux: Running Raspberry Pi OS and Android for IoT Development
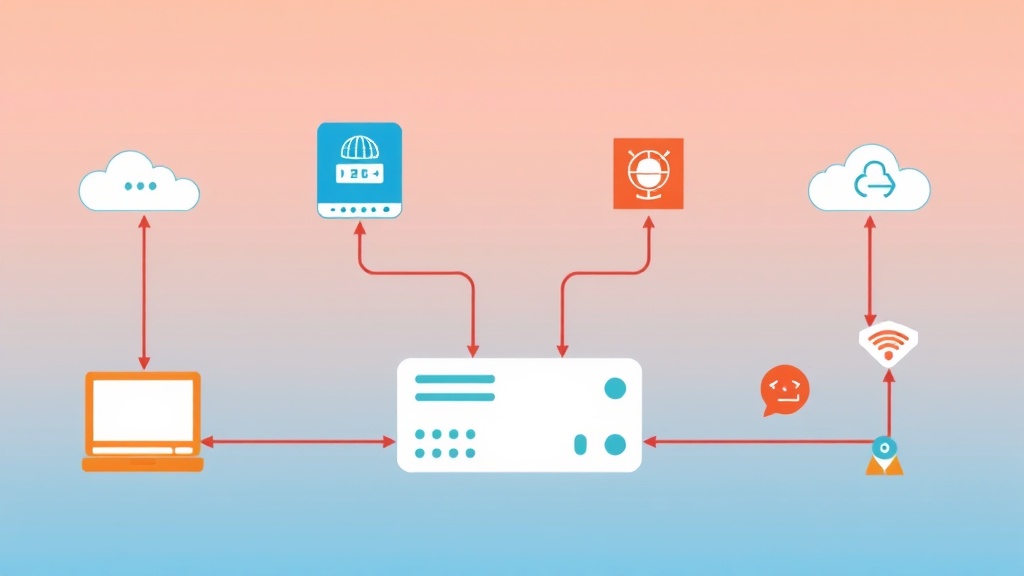
A practical guide to installing QEMU and emulating ARM64 on Linux to run Raspberry Pi OS and Android without real hardware. Covers real-world IoT development workflows: cross-compilation, Docker buildx for ARM64, snapshots, and shared folders.