Posted inDocker
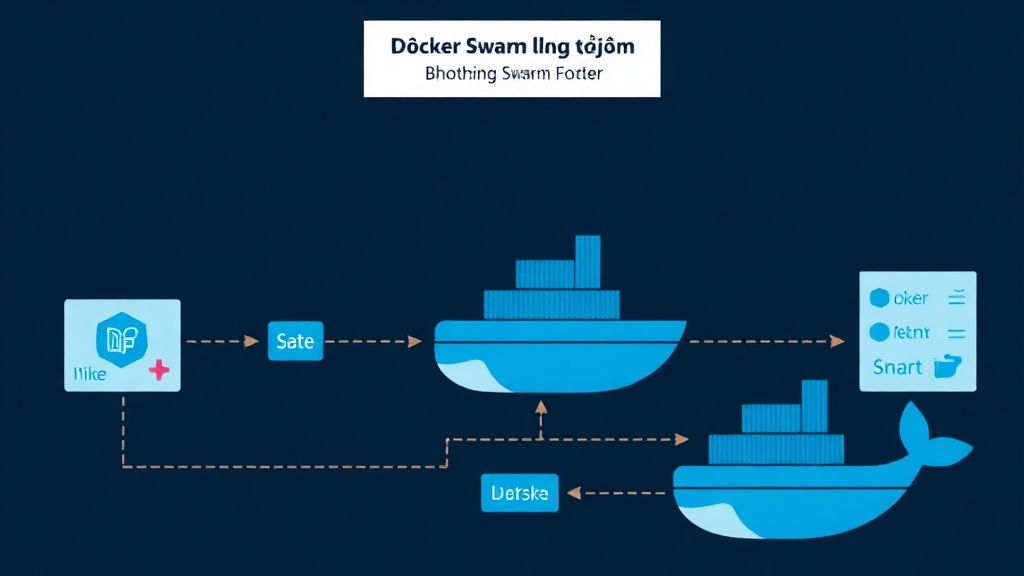
Advanced Docker Swarm: Rolling Updates, Placement Constraints, and Zero-Downtime Deployments
A detailed guide to configuring Docker Swarm for production: zero-downtime Rolling Updates with order: start-first, Placement Constraints for proper workload distribution, and Docker Config/Secret for secure configuration management. Written for those who already know Swarm basics and want to level up to a real production environment without deployment downtime.